Cyber Security System Technology Icons Set Vector. Cyber Security Software And Application, Padlock And Password For Data Base And Information Protection From Virus Line. Color Illustrations Stock Vector | Adobe Stock

The architecture of the cybersecurity knowledge base. DDoS: distributed... | Download Scientific Diagram

Building a base of cybersecurity experts in Indiana - WISH-TV | Indianapolis News | Indiana Weather | Indiana Traffic
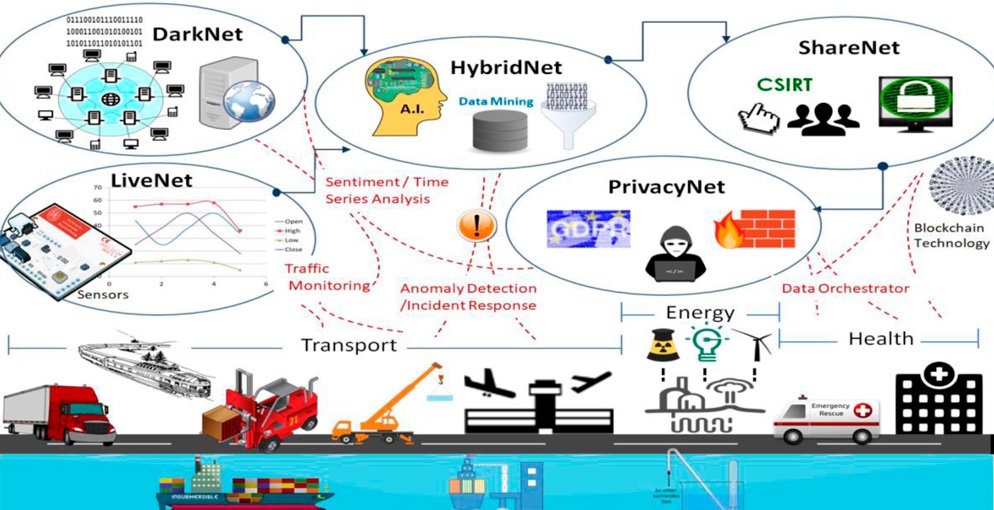
CYBERSANE - CYBER SECURITY INCIDENT HANDLING, WARNING AND RESPONSE SYSTEM FOR THE EUROPEAN CRITICAL INFRASTRUCTURES - Fundación Valenciaport

Companies need to invest more in cybersecurity, 5G to propel internet user base to 25 bn in 2023: Rajesh Pant, Government News, ET Government